The Incident Command System
This article explores the benefits and challenges of migrating the Incident Command System (ICS) to its next level given remarkable advances in enabling technologies, a changing threat, the importance of thinking about response as all risk (multi-cause/multi-agency/multi-organization) and new concepts of operation (CONOPS). Our purpose is to contribute to the dialogue about ICS-Next Generation and provide updates on projects underway that may impact this discussion.
The Origin of ICS
But what is ICS-Next Generation? To understand what it is and what it has the potential to be, we must first visit the history of “ICS-Original” or just plain ICS.
The Incident Command System, as we know it today, started as most emergency management systems do: by necessity caused by a major disaster. In this case, the disaster was the worst series of fires on record in California at the time. The fall 1970 fire siege driven by extremely dry and relentless Santa Ana winds lasted 13 days. Hundreds of thousands of acres burned, thousands of homes were destroyed and many people died, both civilians and firefighters.
The lead fire agencies (federal, state and local) combined with private industry and supported by public and political entities formed FIRESCOPE (see www.firescope.org). This organization developed a standardized system of command and control (C2) that was named the Incident Command System (ICS) and that we know today at the national level as the National Incident Management System (NIMS; see www.fema/gov/nims).
The current ICS delivery model, drawn from the technology base of the 1970s, is time specific and relies on voice-over-radio. It uses lengthy planning meetings and briefings to produce paper-based Incident Action Plans (IAPs). Because of the way these plans are developed and disseminated (i.e., “physically published”), they are victims of the tyranny of distance and time, and do not and have never been able to provide actionable information in a timely manner during a fast-moving dynamic incident.
What has changed during the past 40 years? Why should we consider changing a system that has been used on thousands of multi-risk incidents? The answer is one single word: technology.
Technologies
Applied to Command
While the technology base of the 1970s supported “static” concepts relying mainly on paper and voice-over-radio for information transmission and exchange, the explosion in today’s information and communications technologies, which have found their way into just about every aspect of our daily lives, allows us to think about command and control of incidents as dynamic, streaming events (constant real-time information flow) enabled by computer-based technology. It allows us to think about new levels of commander collaboration and subsequent command and control decision-making activities that were impossible before.
Although there are many ways to look at this explosion in technologies, one way is to examine three major technology themes that are influencing ICS: networking, instrumentation, and command and control. Advances in these three areas have been driven, in large part, by research and development in the U.S. military and have found their way into military C2. How will they influence ICS-Next Generation?
Networking is now a commodity. We can find high-bandwidth network portals in every community (even in our living rooms and favorite coffee shops!) as well as in some of the more remote areas of our regions. Where there is no access to the Internet, we can establish an Internet bubble over incidents using a variety of airborne platforms (the military has a number of these) or through “mesh networks” where the fleet of responding vehicles dispatched to an incident automatically establishes ad hoc networks that reconfigure themselves automatically as the vehicles move about the incident battlefield. Being connected provides access to powerful new applications (“apps” for short).
Instrumentation is becoming pervasive in our daily lives. Modern cars are a good example. Scores of miniature, cheap sensors talk to the car’s computer to instantly analyze and fine tune overall system performance, in some cases dozens of times a second. How soon will it be before radio frequency identification tags (RFID), cheap enough to be woven into clothes we buy at the mall, are woven into every hose so that an engine “knows” about its complement of onboard hose and can communicate that to tactical operational and re-supply functions as needed?
New concepts in command and control that treat battlefield data as “streaming” are changing how military commanders collaborate and solve complex problems. A good example of this is the military’s Command Post of the Future (CPOF) research project developed by the Defense Advanced Research Project Agency and deployed to Iraq with the First Calvary Division in 2004. Fire service personnel were invited to view the system during combat training maneuvers at the National Training Center in the California desert and during actual combat operations in Iraq. MIT Lincoln Laboratory (MIT LL; see www.ll.mit.edu), a federally funded research and development center, has applied and continued these research concepts and has adapted them to emergency response.
Web-Based ICS
The key idea in the MIT LL approach is to use the concept of a Services Oriented Architecture (SOA), an architecture that allows all sorts of apps and data to be plugged in at will from any source (laboratory, commercial vendor, university, firehouse or police precinct, etc). The Department of Defense has spent considerable resources perfecting the SOA concept, and it is readily and freely available to the first responder community for experimentation and use. MIT LL has teamed with CAL FIRE and the sheriff’s office in Riverside County, CA, and has been testing this concept for more than two years. It is now being scaled up to other departments and agencies in Southern California to include San Diego County agencies.
Looking Ahead
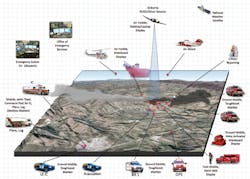
Does work like this give us a glimpse of what ICS-Next Generation may look like? The approach that is taking shape is open, non-proprietary, web-based and can be accessed by any standard computer (any computer type and any operating system) through the web (any browser). Myriad operational data can be transmitted in real time between operators. This includes maps of all types, operator-to-operator sketch, chat, pre-plans, incident action plans, dispatch and current resource data, weather information, historical fire data, and automatic vehicle and personnel location data (AVL/PLI) as examples.
For instance, apps have been developed that allow ground units to access real-time aerial intelligence data gathered from air assets as well as allow the ground commander to control the aircraft camera from the ground using a simple joy stick so that the commander can see what he wants to see.
All data can be recorded for future use for both historical and legal needs. Possibly even more important is the training value of creating notional emergency scenarios and studying historical incidents using the same technology.
This next generation of ICS will obviously provide a greatly improved benefit to the operator in the field, but will also provide additional value added to the overall emergency response community. Operational commanders at national, state and regional levels can access real-time information on an incident or multiple incidents to enhance strategic decision-making. Involved political leaders can be kept informed of current threats and ongoing operations, and the public can be notified of emergency operations both current and proposed that may affect their safety and welfare.
Continued development, testing and refinement of these concepts will be conducted in the Southern California test area and other selected regional locations in upcoming months. This development will take place through both training exercises and through response to actual all risk incidents. Challenges in scaling to extreme-scale incidents (e.g., massive natural disasters), easy-to-use operator interfaces (little to no-training required), and simple but powerful user commands that are suited to the “tired-dirty-hungry” responder will be high on the research agenda.
BILL CLAYTON is the chief of the Sycuan Fire Department in San Diego County, CA, and previously served as a division chief for CAL FIRE. He has 48 years experience in emergency response.
DR. JACK THORPE is a retired U.S. Air Force colonel who served as a research-and-development officer for 26 years and managed advanced technology projects at the Defense Advanced Research Projects Agency.